In another finding that could expose developers to the increased risk of a supply chain attack, it turns out that nearly a third of the packages in PyPI, the Python Package Index, trigger automatic code execution upon download.
“A troubling feature in pip/PyPI allows code to be executed automatically when developers are simply downloading a package,” Checkmarx researcher Yehuda Gelb said in a technical report published this week.
“Also, this feature is alarming given that a large proportion of malicious packages we are finding in the wild use this post-installation code execution feature to achieve higher infection rates.”
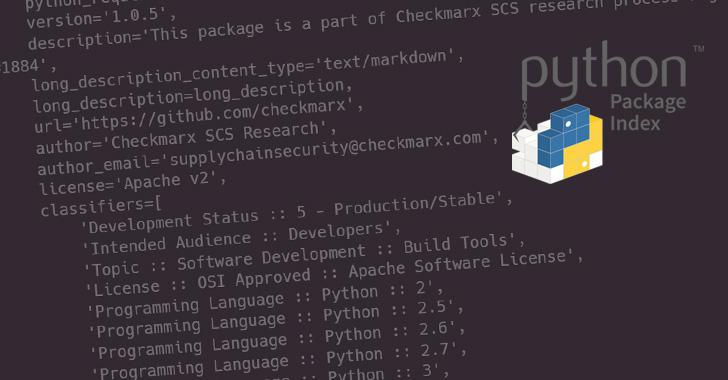
One of the ways packages can be installed for Python is by running the “pip install” command, which, in turn, calls a file called “setup.py” that comes with the module.

“setup.py”, as the name implies, is a setup script used to specify metadata associated with the package, including its dependencies.
While threat actors have used the inclusion of malicious code in the setup.py file, Checkmarx found that adversaries could achieve the same goals by running what’s called a “pip download” command.
“pip download does the same resolution and download as pip install, but instead of installing dependencies, it collects the downloaded distributions in the provided directory (defaulting to the current directory),” the documentation says.
In other words, the command can be used to download a Python package without having to install it on the system. But as it turns out, running the download command also runs the aforementioned “setup.py” script, resulting in the execution of the malicious code contained within it.
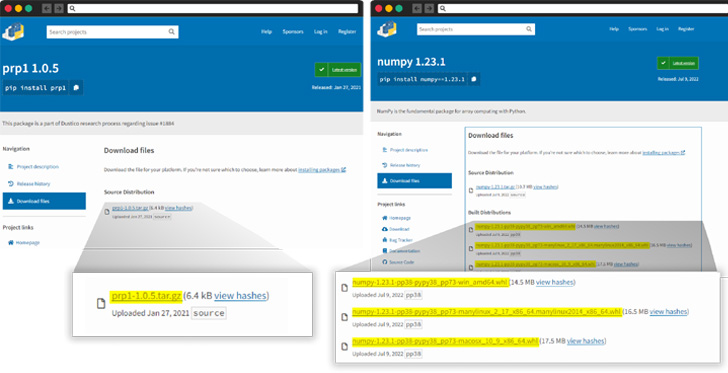
However, it’s worth noting that the problem only occurs when the package contains a tar.gz file instead of a wheels (.whl) file, which “cuts the ‘setup.py’ executable from the equation.”
“Developers who choose to download, rather than install, packages reasonably expect that no code will run on the machine after downloading the files,” Gelb noted, characterizing it as a design problem rather than a mistake.
Although pip defaults to using wheels instead of tar.gz files, an attacker could take advantage of this behavior to intentionally publish python packages without a .whl file, leading to the execution of malicious code present in the setup script.

“When a user downloads a python package from PyPi, pip prefers to use the .whl file, but will fall back to the tar.gz file if the .whl file is missing,” Gelb said.
The findings come after the US National Security Agency (NSA), along with the Cyber Security and Infrastructure Security Agency (CISA) and the Office of the Director of National Intelligence (ODNI), issued guidance on securing the software supply chain.
“As the cyber threat continues to become more sophisticated, adversaries are beginning to attack the software supply chain, rather than relying on publicly known vulnerabilities,” the agency said. “Until all DevOps are DevSecOps, the software development lifecycle will be at risk.”



